A short while ago I stumbled upon an interesting Hacker News conversation…
Intrigued by the challenge, I decided to implement the theory as a WordPress plugin for all to use. So here’s the gory details…
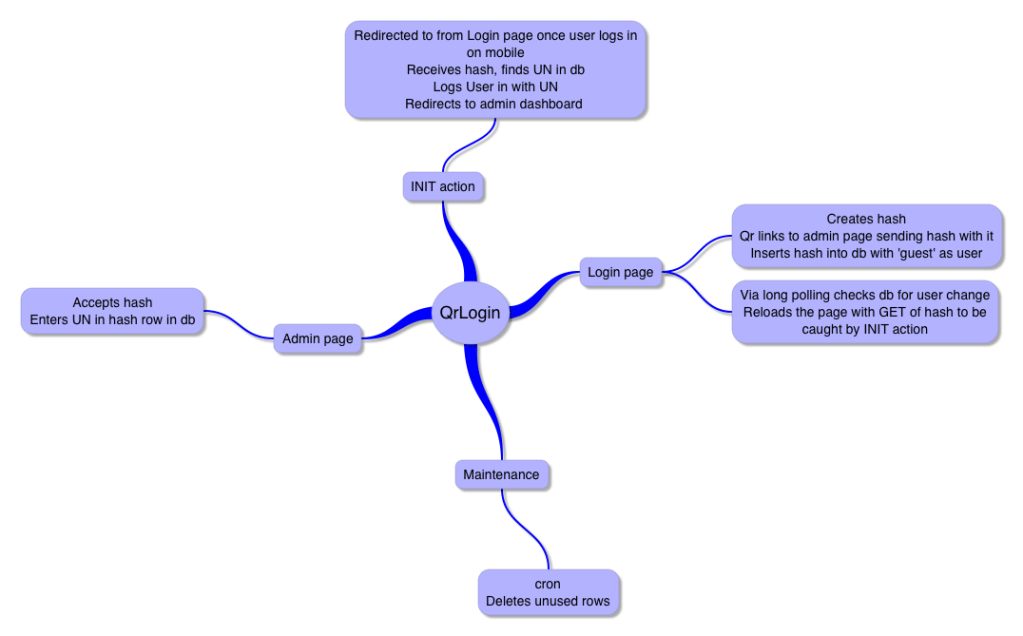
The Flow
- User visits Login page
- Login page Generates unique hash, saves hash to the database
- Login page Creates QR code of a link that GET posts hash to the Plugin’s admin page
- Via long polling **Login page **waits for a username to be inserted into the row in the database that has the page’s active hash
- User scans QR code with mobile device and which is sent to Plugin’s admin page on mobile with along with the active hash posted via GET
- In WordPress, the User must be logged in to reach Plugin admin page by definition
- The Plugin admin page records the username to active hash in the database (the GET posted hash)
- The Login page sees a change in active hash’s row of the database and reloads the page with a GET post of the active hash
- Using the WordPress action init the page receives the hash, finds row of active hash in the database and pulls the username, it then removes the hash from database so it can’t be reused
- The page then logs in the User using the username pulled and redirects the User to the WordPress Dashboard
Notes
Alone, this isn’t a solution to never having to remember your passwords again. Your mobile browser has to have the logged-in cookies for it to work completely without password.
Why is it still useful? Well, everyone goes everywhere with their cellphones now, but with today’s mobility it means that you’re likely to find yourself with an urgent idea to post to your blog, and not wanting to type it out with your thumbs on your mobile. So, borrow Aunt Sally’s computer – that by all chance has thousands of suspicious apps, key loggers and, by the way, is running Vista – and to log in just scan away!
Ideally, it would work great with an app built to complement it that would scan the qr code, save your passwords, and log you in automatically if the local cookie had expired… Perhaps that app is in the works… Comment below if you’d like it and I may be swayed to create such a monster. Perhaps tiqr might want to gang up…
Is it secure? I’ve put several checks in place to make sure it is.
- Username/password are never passed back and forth, only the unique hash.
- Hash is removed from the database once it’s used, old hashes that haven’t been used can’t be unless the database is hacked, but then you have bigger issues.
- All database queries of the hash have been escaped to prevent XSS attacks.
- nonce added to ajax call.
- nonce and confirmation added to on mobile end to prevent CSRF attack.
I’m pretty sure that covers security. Anything else needed?
Suggestions? Comments? You know where that goes…
Special thanks to…
- 5 tips for using AJAX in WordPress
- PHP jQuery AJAX Javascript Long Polling – although the long polling solution I worked out with WordPress’ AJAX isn’t perfect yet.
- And of course @PeterLegierski for the original post on HN.
You must be logged in to post a comment.